AI TrustID
TrustID
This is a system for identity identification and verification. It can determine if individuals in two photos match each other, verify the "liveness" of the photos, and identify the person captured in the photo. A distinctive feature of the solution is that the entire system, including the database, is hosted on your server (on-premise), ensuring complete data security. Let's further examine the three main algorithms that form the basis of the system's operation: Comparison, Liveness, and 1:n Search.
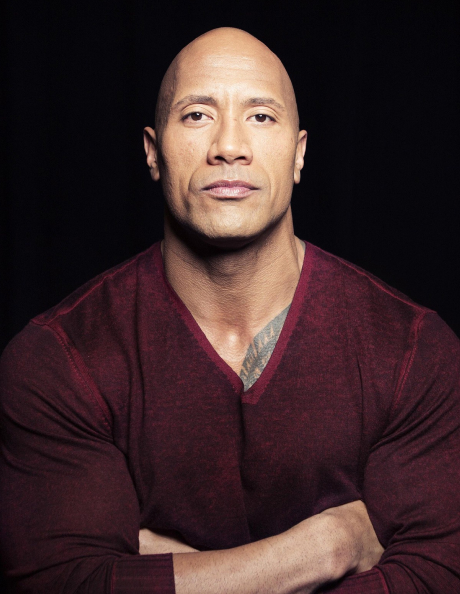
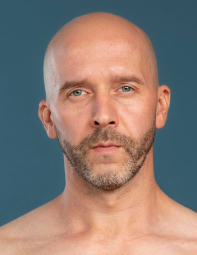
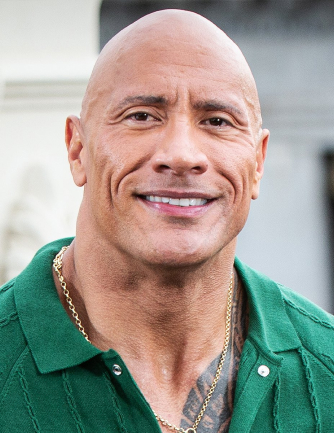
Comparison
This algorithm compares people in 2 photos and answers whether it's the same person in both photos or they are 2 different people. The algorithm works not with the photos themselves, but with so-called photo vectors.



On the face, 512 reference points are taken, and lines are drawn based on them.
These lines from two photos are compared to each other, and a conclusion is drawn regarding their correspondence. The reference points are chosen in such a way that age-related changes, glasses, beards, etc., do not interfere with determining whether the same person is depicted in the two photos.

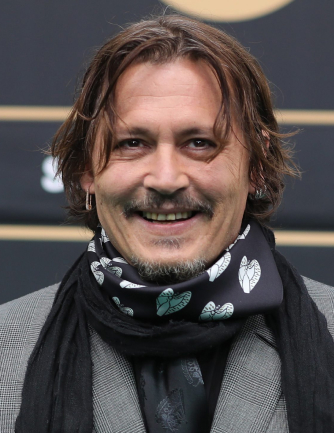

Moreover, such a quantity of points prevents confusion between twins.
Liveness
To determine that the person accessing your application is indeed its owner, two aspects need to be verified:
Camera photo matches your existing owner photo



Camera photo - it's a photo of a real person, not a photo of a photo



The algorithm's function essentially involves artificial intelligence making decisions about the "liveness" of photos, and our task is to teach AI to accurately distinguish real photos from spoofs. How does this happen? Dozens of individuals specially trained by us gather sets of hundreds of thousands of sorted real and fake photos (datasets). These prepared datasets are then loaded into AI for training. The AI identifies common features among all real photos and common features among all fake photos, as well as features that differentiate real photos from spoofs. It's worth noting that these features are often completely imperceptible to the human eye. Once the model training is complete, testers take over. These are not the same people who collected the datasets. They are unaware of the fake materials on which the AI was trained and try various methods to deceive the system, attempting to have it accept a fake photo as real or, conversely, reject a real photo as fake. If this occurs, the system continues to be trained specifically on such photos. New datasets are assembled, loaded into the models, and the training process continues.The uniqueness of AI with machine learning lies in the fact that even when operating in real products with real photos and real attempts at deception, the system continues to learn and improve even in the absence of any erroneous triggers.














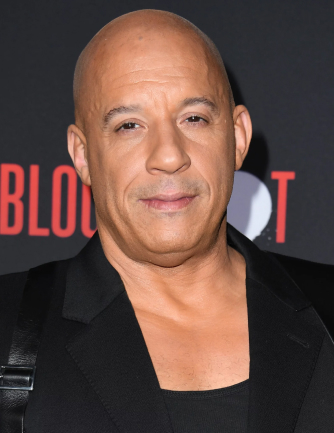
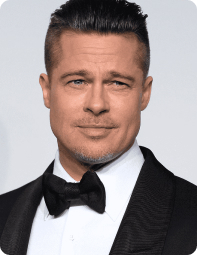
1:N Search
Another capability of TrustID is its 1:n search feature, where a face is searched for in a database of previously uploaded images, and the output result is a set of similar faces, the similarity of which exceeds a certain threshold. For example, if we need to see all the photos in a database of criminals that are similar to a suspect by more than 70%, and let's say there are only three such matches. The first is similar by 98%, the second by 73%, and the third by 71%. TrustID will output the results in descending order. Searching among 2 million registered individuals in the database takes only 0.6 seconds. The speed of the search is facilitated by our proprietary algorithms for facial feature extraction and the immediate rejection of dissimilar individuals based on these features in batches. For instance, all photos with dissimilar noses are immediately filtered out, even if the other features are very similar.
Additionally, there's the option to check photos not against the entire database, but against a pre-selected group. To do this, when uploading a photo to the database, the user's group affiliation must be assigned immediately. For instance, to check students entering a classroom, you can search for a specific student within their class.
By acquiring our TrustID solution, you gain a powerful and secure tool for identifying and verifying your users and visitors.






Our other products

AI SmartEye

Vision Mobile and Web SDK

